Okta: Product, Business Model, Growth
Sign up for ARPU: Stay informed with our newsletter - or upgrade to bespoke intelligence.
In this article, we will look at Okta by unpacking its trajectory, its go-to-market strategy, key financial metrics and what could be next for this IAM leader.
Founding history
In 2008, as the world was entering the most severe economic downturn since the Great Depression, Todd McKinnon, a highly successful senior executive, responsible for engineering at Salesforce, realized his career had stalled.
Through his work, he could see that the great enterprise shift from on-prem to the cloud would soon unfold in a major way. It was a time when cloud-based collaboration apps, business apps, and infrastructure started to proliferate, and an entire generation of cloud-based companies relying entirely on AWS came to life.
McKinnon had a premonition that many more tools and platforms would be required to support this shift. So he wanted to quit his well-paid job and start a company that would build a monitoring system for other cloud applications.
However, the announcement of his intentions did not go down well at home. Todd and his wife Roxanne had a six-month old daughter, he was just diagnosed with diabetes and the world was on fire. Job security was of key importance.
So Todd drew on his engineering instincts and developed a 13-page presentation for his wife entitled “Why I’m not crazy”, laying out the vision for the shift from on-prem to cloud computing. He uncovered a range of possible scenarios, from worst - he fails and returns to work, to best - he takes the company public after 5-10 years at a valuation of $50 to $100 million. His presentation also pointed out that great companies such as Microsoft and Oracle were started during bad economic times.
Eventually, he won the persuasion battle, resigned from Salesforce and teamed up with co-founder Frederic Kerrest.
The pair quickly realized that application monitoring was a dead end (the initial name Saasure fortunately also did not fly) and pivoted to identity management, adopting a meteorological term Okta which pilots use to determine the scale of cloud cover.
During data center days, companies could easily log into applications using Microsoft Windows. The entire identity management industry was asleep, as everything was embedded in other platforms like Oracle or Microsoft.
But once mobile came along, an exponential explosion in the number of computers, applications and users made it necessary to unlock all of them in a simple and secure way.
As Salesforce, Workday, Box and others all came from the cloud, the companies struggled to log into all of them.
Todd knew enough about the architecture and other things that would need to be implemented to solve this pain point. He also realized that solving it would allow his company to evolve into a standalone platform.
In the first couple years, Okta was able to build the product and it worked. But it came too early. There was not enough cloud for Okta to succeed.
2011 was a particularly difficult year. The company was already backed by Andreessen Horowitz and Floodgate. The world was watching. Before their Series B round, however, they missed the net new bookings target by 60%. And if it wasn’t for Khosla Ventures who pulled through on the term sheet, it could have ended badly.
As Ben Horowitz put it:
“Faced with a prospect of running out of cash and no raise, it would have been easy to hide from the problems, make excuses or give up. Todd and Freddie felt the pressure but they did not succumb to it. Reworked their strategy, improved the team and found a way out."
Just a year later, the market caught up. More applications made the problem really painful and the product became good enough. The company was off to the races.
Ever since crossing the chasm, it has been growing.
The company went public in 2017 and currently has a market cap of over $13 billion. It has more than 15,000 customers across multiple verticals and serves 30% of the Global 2000 companies.
“Looking back on this, it all seems like a good story now,” McKinnon said about the entire experience “but it was pretty nerve-racking.”
First product
The Single Sign-On accomplished a very tactical purpose. It made it super easy to log into cloud applications with a Windows password. An employee of any given company would simply type in a Windows password and would get into Salesforce, Box, Workday or any other cloud application that was not on the company’s network.
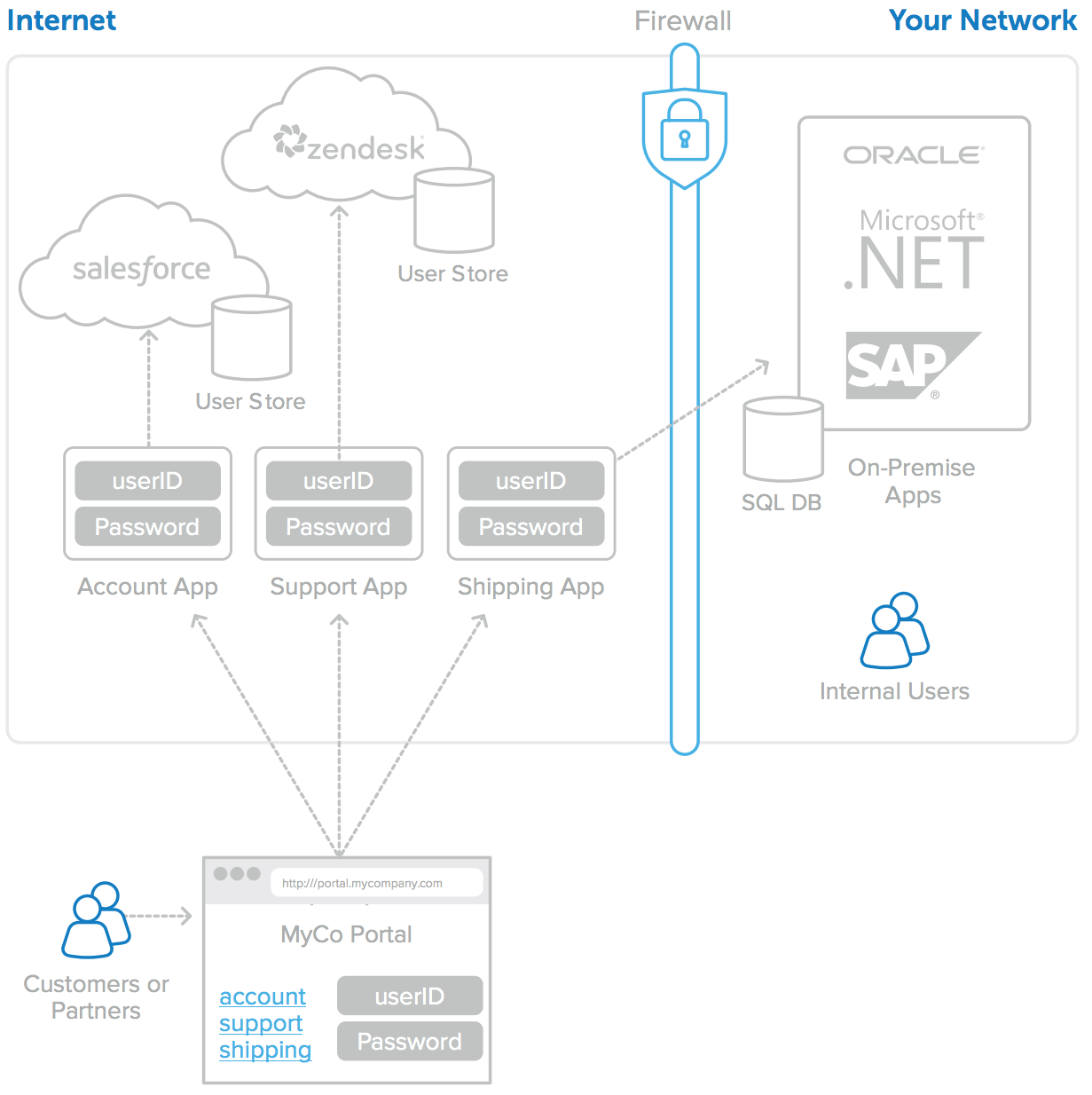
The product also solved a second pain point, by moving from a distributed to a centralized system.
At one point or another, all of us experienced not being able to log into an account, where every single device would simply not recognize us and we had to re-authenticate our way back in, by resetting our password or entering a new six-digit code. This process happened in a single application on a local database.
As Okta came along, it could do this process centrally. Okta has a meta map of all the applications one person has access to and the credentials required for authentication. This authentication happens with Okta which then must handle the challenge of integration by handing off this authentication to all the disparate computers and applications.
Before the login occurs, Okta keeps the different user records and directories in sync across the different systems. Depending on the company’s policy, it then says who are the right people that can access which application from which device.
Moving to a centralized system and making it easy to integrate all of the applications in a given environment were the two difficult challenges that Okta solved. These two variables made the initial product valuable.
Thanks to this, Okta became the gateway for companies to manage the access to enterprise SaaS platforms and for users to access them, while gaining unique insights into the application usage patterns on top of it.
GTM Motion
Okta’s main focus is to acquire and retain customers, increase their spending, cross-sell and up-sell additional and new products, and expand customers’ use of the platform for workforce or customer identity.
The company uses a land-and-expand sales model, directly through field and inside sales teams, and indirectly through a network of channel partners, such as resellers, system integrators and other distribution partners.
Historically, Okta’s GTM motion was very much a top-down affair, with the sales team targeting C-level executives at Global 2000 companies for them to take over identity management concerns.
However, less than a year ago, Okta acquired Auth0, a developer-facing SaaS platform and SDK which developers use to embed authentication and authorization features into their applications. Basically, Auth0’s value prop in the customer identity management space is similar to that of Stripe for payments or Twilio for communications. The company provides developers with features, so they do not have to build them from scratch.
With a heavy focus on developers, Auth0 had a diametrically opposed bottom-up GTM strategy. Following the acquisition, it was not clear how the two would be reconciled.
Even if there were some early wins in cross-selling, with a great example from the last quarter, when Carvana, the e-commerce platform for buying and selling used cars, and a long-standing Okta workforce customer, expanded the partnership and selected Auth0 to provide its partners and dealerships with access to its marketplace to widen the selection of vehicles.
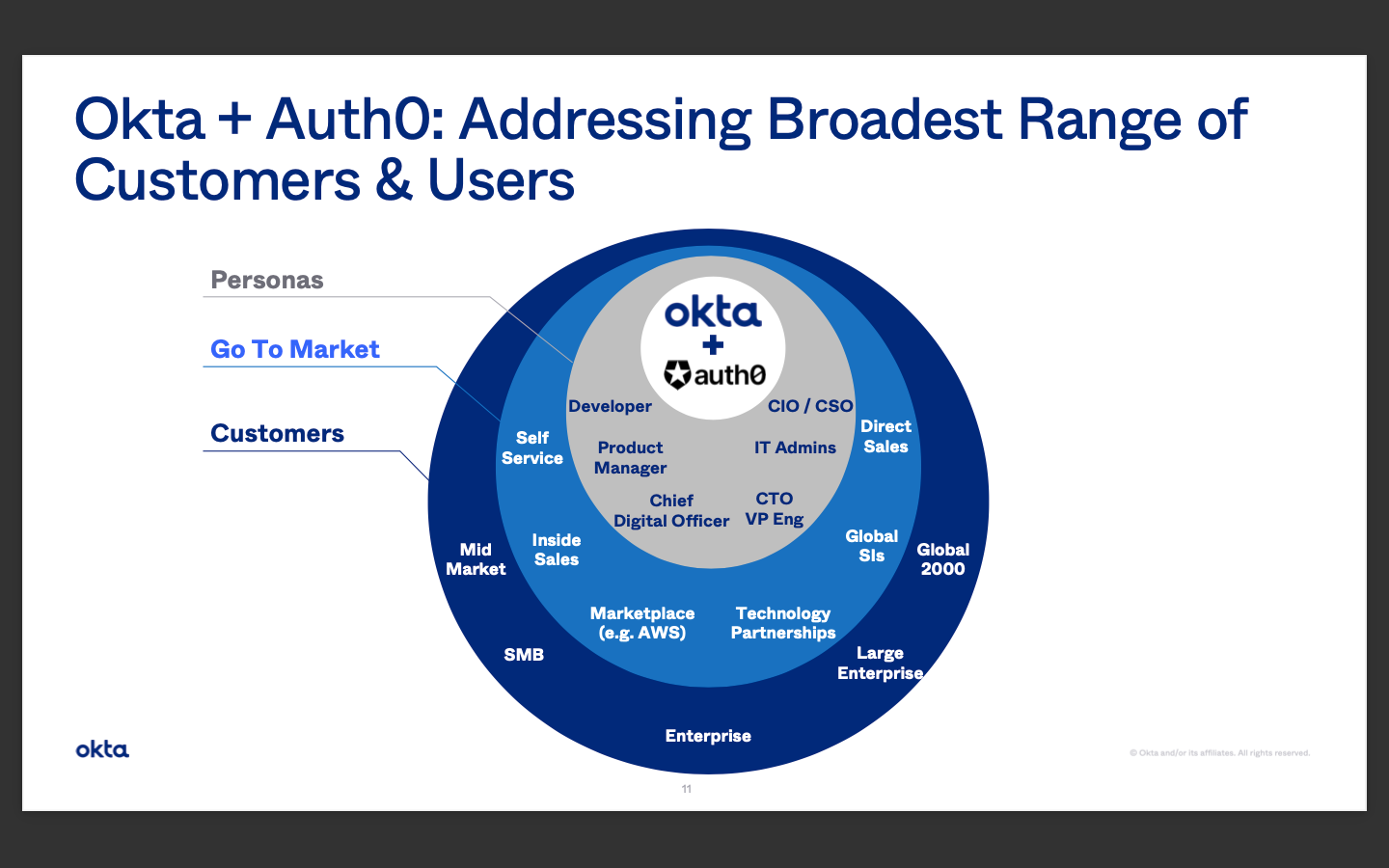
However, during the last conference call, the picture became clearer. McKinnon has announced that the GTM organization has been unified under Susan St. Ledger’s leadership. Susan has led major growth initiatives at Splunk and Salesforce and claims their high growth motions are repeatable. She is big on attacking customer information management, expanding internationally and leveraging global system integrators and cloud marketplaces. One team will now sell both Okta and Auth0 and aggressively pursue the SIEM market, from top-down and bottom-up.
Okta was always criticized for selling almost exclusively on US soil and ignoring international expansion. Slowly but surely this weakness is being rectified, as international revenue grew 97% in the fiscal year 2022 and now amounts to 20% of all sales. Some of that growth is directly attributable to Auth0, as 40% of their revenue is international.
Okta views the worldwide expansion as a long-term opportunity as organizations outside the US embrace the transition to cloud computing, and international organizations consolidate within their global locations.
Okta’s evolution
From founding until now, the company has gone through four major chapters.
The first was the initial build out of the product and the subsequent struggle which unfolded until 2011, all the way to crossing the chasm, surpassing the ARR target for the first time and growing since.
The second chapter came in 2014 when Microsoft announced a product which was an Okta killer. According to McKinnon this announcement made Okta step their game up and certified identity management as a standalone category. After 2014, Microsoft also propelled a great push to the cloud with Azure and the next few years were really good for the company.
The third chapter came after the company went public in 2017 until 2020. During this time, Okta was scaling fast. It was also a time when more and more of Okta’s customers came to the company and said they would like to use it not just for their employees but also for their customers, as they login to a support site or a mobile app.
So Okta moved to the second biggest part of their business which is customer identity management. CIAM is now close to 40% of Okta’s business and grows much faster than workforce identity. So for example, if you log into the MLB app, it is done through Okta.
The fourth chapter came after a wakeup call, when Okta lost its leadership position in the Gartner’s Magic Quadrant for identity access management in 2020 to Microsoft.
The report criticized the company for the lack of geographic diversification, the basic nature of their customer identity management product, and the absence of fuller features such as governance.
The company moved quickly to rectify these by acquiring Auth0, announcing a new product line up and doubling down on international expansion. These moves resulted in Okta regaining its leadership position for the subsequent year.
In light of all the changes it has introduced, Okta has now entered its fifth phase which will unfold in a major way in the next few years.
As the growth of its legacy workforce business is waning and constitutes a drag on top-line growth, Okta rightly leaned into the faster growing CIAM segment with the Auth0 acquisition, the GTM motion consolidation and international expansion. These steps already made the company the top name in CIAM.
The company has also completed a C-suite reshuffle. Last year, after their long-standing CFO retired, they botched his replacement by appointing Mike Kourney who previously headed Okta’s Audit committee and departed after just one quarter, as a result of a “culture clash”. Now Brett Tighe who previously served as Okta’s Senior Vice President of FP&A and Treasury has been appointed as the CFO.
Susan St. Ledger’s inner circle has also been bolstered with appointments of new CMO, CRO and CDO all reporting directly or indirectly to her.
As the company progressed, it brought new products to the market.
Okta developed the Universal Directory which is a centralized, cloud-based system of record to store and secure user, app and device profiles for an organization and allows it to track users and access rights.
The company also offers Multi-Factor Authentication for an extra layer of security and Lifecycle Management to automate the provisioning of users and changing access rights, as the workforce evolves and adjusts.
In 2018, Okta also acquired ScaleFT to enhance the company’s Zero Trust security capabilities. As a result, it offers two additional products, Access Gateway which enables organizations to extend the Okta Identity Cloud from the cloud to existing on-premises applications (Hybrid IT) and Advanced Server Access which offers Zero Trust for infrastructure access.
Revenue breakdown
Okta operates its business as one reportable segment. It derives subscription revenue from fees for access to and usage of their platform. This revenue is driven primarily by the number of customers, users per customer and the products used. Okta typically invoices customers in advance in annual installments for subscription in a classic SaaS model.
It also derives professional services revenue from fees for assisting customers in the use of their products such as application configuration, system integration and training services.
For the fiscal year 2022, total revenue was $1.3 billion, an increase of 56% year-over-year with subscription revenue amounting to $1.25 billion. On an Okta standalone basis (excluding $140 million attributable to Auth0), total revenue grew 39%.
The most important distinction in the breakdown of revenue is the divide between Okta’s two largest business segments which are workforce and customer identity management. Workforce is now 63% of total ACV but grows only at 37% year-over-year and is, actually, the biggest drag on Okta’s growth.
The combined customer identity is now the primary growth engine. It constitutes 37% of total ACV and is growing much faster than workforce identity at 59%. What is even more interesting is that Auth0 grows much faster at 81% relative to Okta’s standalone growth of 47%.
RPO remains strong at $2.69 billion for an increase of 50% year-over-year, while total calculated billings stand at $1.72 billion, an increase of 76% year-over-year. Dollar-Based Net Retention Rate was fairly flat at 124%.
For 2022, Okta generated losses of $848.4 million (an increase from $266.3 million in the year prior). Okta’s accumulated deficit is $1.8 billion.
Net cash from operations was $104 million, or 8% of total revenue, compared to $128 million, or 15% of total revenue for 2021. Free cash flow was $87 million, or 7% of total revenue, compared to $111 million, or 13% of total revenue for 2021.
The losses were largely attributable to higher operating expenses related to Auth0, increased investments to scale, and bigger headcount in sales and marketing, and R&D.
Okta now has 15,000 customers. 3,100 have ACV exceeding $100k (59% growth year-over-year), 597 have ACV exceeding $500k (62% growth year-over-year) and 197 over $1 million (58% growth year-over-year).
What’s next
It is clear that Okta is currently in a flux.
The ongoing cloud adoption, digital transformation and Zero Trust security are three strong structural tailwinds for Okta.
However, the quality of next steps in this new chapter will determine whether the company can regain its hypergrowth mode and eventually reach profitability.
And there are multiple variables on which the company’s success hinges going forward, including how the ongoing integration of Auth0 and Okta plays out, whether their efforts to ramp up international sales will bear fruit, the quality of their new products in PAM and IGA (more on that below) and Okta’s ability to translate them into viable revenue streams, and, most importantly how they decide to play in the Zero Trust security space.
Zero Trust
Zero Trust is a new security paradigm that will grow ever more important in the current environment. More than 80% of the Global 2000 companies have now declared initiatives around Zero Trust security.
As mentioned, Okta has Access Gateway and Advanced Server Access as the relevant products here. However, both are not given primary attention. It remains to be seen whether Okta simply wants to offer helpful tooling to its Zero Trust partners or actually move into the space as a legitimate player. Another important point is that some of Okta’s Zero Trust partners appear to be able to circumvent Okta’s SSO, as they create their own interfaces for identity access management. Given the importance of this structural tailwind, Okta’s steps here will need to be monitored closely.
PAM
In light of the wake-up call of losing leadership in the IAM space, Okta announced it will move into two adjacent markets, claiming these will add $15 billion to make up the $80 billion TAM they are going after.
The first is the Privileged Access Management (PAM) which is about controlling access to on-prem or cloud systems for administrators who can make system changes, deploy apps, or create cloud infrastructure. CyberArk and BeyondTrust are the leading players here. For Okta, it is still early. During the last earnings call, the CEO announced that the company is making progress developing new PAM functionality and will have more news on the developments over the course of this year.
IGA
The second is Identity Governance and Administration (IGA) which encompasses orchestrating and tracking access rights of users in a given application. While the administration part is already handled through Okta’s Lifecycle Management as it allows to track and automate workflows, they still need to work on governance (as per the Gartner critique) to ensure compliance with business policies and automate processes to minimize risk.
They have already deployed a beta version of the product in Q3 2022 and have confirmed on the latest call that the feedback has been very positive. The CPO has prioritized enhancing the product and Okta will now initiate early access to a limited number of customers. They expect Okta Identity Governance to launch in North America by midyear and globally by year-end.
Finally, as the new CFO announced his priorities, he underlined his intention to ensure that Okta achieves at least $4 billion in revenue in 2026 with organic growth of at least 35% each year and a 20% free cash flow margin.
If Okta wants to go back to higher growth (their average revenue growth in the past five years was 59%), it needs to:
- Execute on a seamless integration of Auth0.
- Deliver on the combined top-down and bottom-up GTM motion.
- Ramp up international sales.
- Deliver flawless PAM and IGA products that turn into strong revenue streams.
- Crystalize their play in the Zero Trust security space.
I hope you enjoy this article! Hit the button below to have insights and stories like this delivered to your inbox!